Azure Dev College - Kubernetes on Azure
Second day of Remote Azure Dev College, today we will discover Kubernetes hosted on Azure and all it's features.

The fist day was very interesting, as some people pointed out, we didn't actually learn something new around Containers, we got all the commands in more depth and got a bit more into learning what containers actually are and where they are coming from.
Today Christian Dennig is giving the presentation on Kubernetes, where it is coming from, what the idea is and afterwards we will do some hands-on exercises.
In the most tutorials, the trainees, get their hands dirty with Minikube, as it is the simplest to setup locally without much knowledge.
Clearly in the beginning of the training it was stated that the use of Kubernetes should be evaluated before hand. Kubernetes is bringing a huge complexity to the table. Rule of thumb should be if you are under a 7-10 container infrastructure, it is not recommended to setup a Kubernetes cluster. There are many tools out there to setup up every kind of Environment. Kubernetes helps you steer the ship more effortlessly, but we will have to build the ships and harbor first.
If we only want to sell fish or bring the goods up the river, we will not have to deal with the complexity Kubernetes will bring to the table.
Day 2 consisted of these Challenges which were setup to build an infrastructure which consists of an app to add, remove, edit, search and an UI built with vue.js.
All of these challenges will be built in and on azure but mostly through the Azure CLI.
Challenge-0 was a prerequisite and guides us through the installation of the needed tools.
In Challenge-1 we will create our first Kubernetes Cluster, with a few commands through the azure-cli we create our resource group, with the help of AKS we are creating our first cluster. Since AKS comes with the kubernetes-dashboard installed by default we also write our first deployment .yaml to enable access to the cluster. This approach shouldn't be used in a production environment, since it opens up a way to access the cluster from the outside world.
Challenge 2 will bring us Basic Kubernetes Concepts. We start of by creating a container registry as Azure provides its own service for that, the Azure Container Registry. Which can also build docker images in the cloud, I didn't know that. After building and running our first self-made image in a pod, we are also deploying an MSSQL instance into the pod. We get more ways to inspect the started pods and learn more about the terminology.
This Challenge is huge compared to yesterday challenges, I guess Basic Concepts is already an huge field in Kubernetes. We learn about an Ingress, with this awesome google spreadsheet, and how we will introduce it as proxy to all our services in the backend. That will give us the opportunity to have a single gateway to our worker node. Traefik is also in the list and I think I did setup my server as a 'stand-alone' Worker Node, farfetched I guess but it shows us kind of the scalability of a Kubernetes Cluster.
Congratulations, you have deployed a full-blown application to Kubernetes with a SQL server running inside the cluster. As you might guess, there are a few things now that need to be adjusted. E.g. we added some of the configuration settings - even worse, passwords! - "hard-coded" to manifest files. Also the endpoint configuration for the UI has been baked into the image. In the next challenge, we will adress these issues by using KubernetesConfigMapsandSecrets. You will learn how to configure your application "from outside" by using standard Kubernetes objects.
This is what we will tackle in Challenge 3, by fixing the "hard-coded" settings and passwords. Both can be configured by literals, give through kubectl, or by passing a file to the deployment.
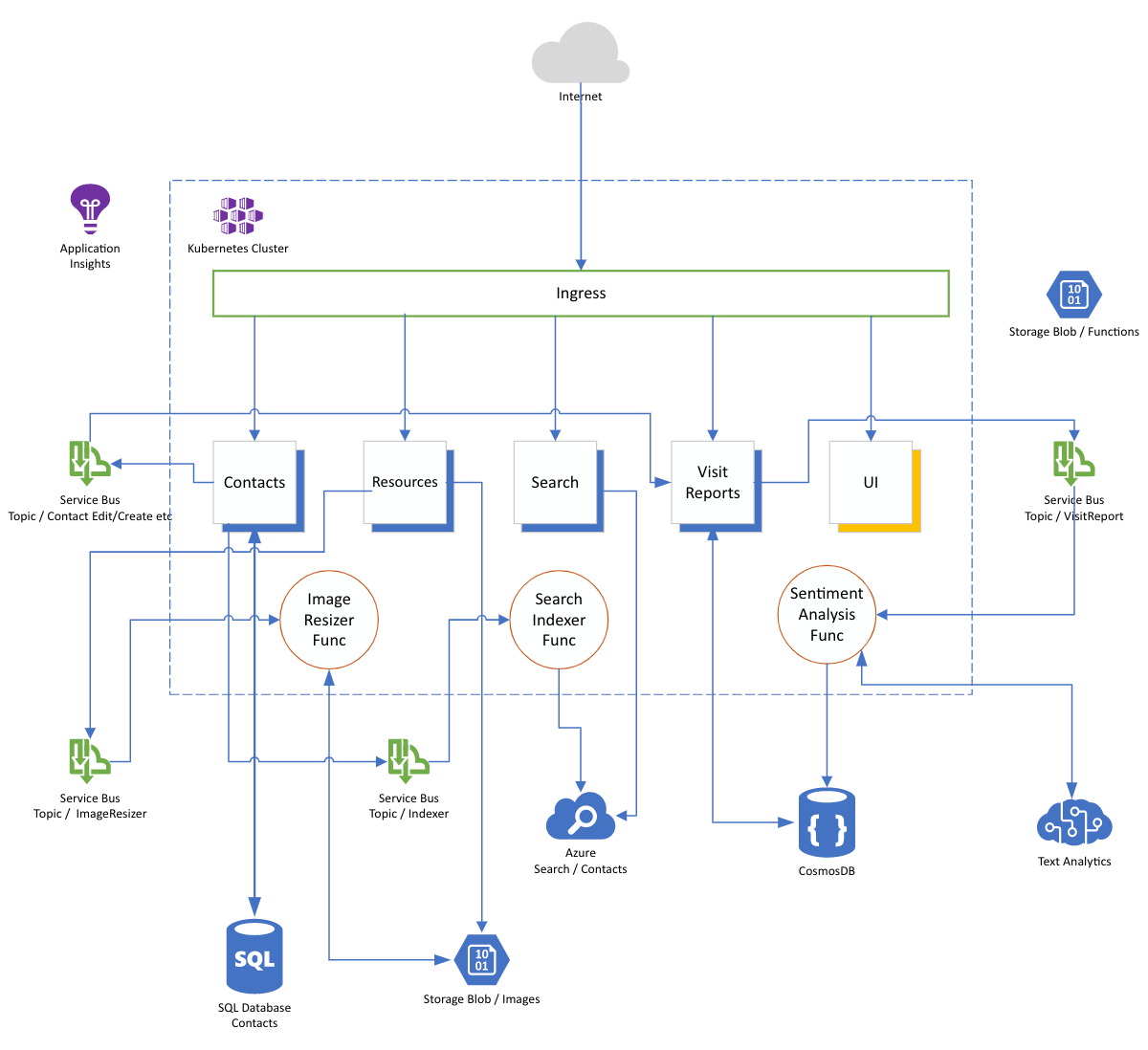
In Challenge 4 we will deploy the Simple Contacts Management app as in this picture
We will use Terraform to create the Azure infrastructure, which is a very popular tool in the "Infrastructure-as-Code" space. Now we will just pass deployments into the created infrastructure and we will have it available at portal.azure.com.
The Bonus Challenge shows us how to setup let's encrypt for all of our services, very helpful. On this server I achieved it with the help of Traefik!
In the end our Kubernetes Cluster should look like this as described in the image above.
$ kubectl get deployment,pods,service,endpoints,ingress
NAME READY UP-TO-DATE AVAILABLE AGE
deployment.apps/ca-deploy 2/2 2 2 23h
deployment.apps/frontend-deploy 2/2 2 2 22h
deployment.apps/resources-deploy 2/2 2 2 23h
deployment.apps/resources-function-deploy 2/2 2 2 22h
deployment.apps/search-deploy 2/2 2 2 22h
deployment.apps/search-function-deploy 2/2 2 2 22h
deployment.apps/textanalytics-function-deploy 2/2 2 2 22h
deployment.apps/visitreports-deploy 2/2 2 2 22h
NAME READY STATUS RESTARTS AGE
pod/ca-deploy-75bcd947f8-gbppf 1/1 Running 0 23h
pod/ca-deploy-75bcd947f8-mpkdd 1/1 Running 0 23h
pod/frontend-deploy-76d6fdfd85-mpcnj 1/1 Running 0 22h
pod/frontend-deploy-76d6fdfd85-xwvfv 1/1 Running 0 22h
pod/resources-deploy-7567764b6b-fbwmg 1/1 Running 0 23h
pod/resources-deploy-7567764b6b-pkpvg 1/1 Running 0 23h
pod/resources-function-deploy-5f8487bc8f-96nq7 1/1 Running 0 22h
pod/resources-function-deploy-5f8487bc8f-b7b5z 1/1 Running 0 22h
pod/search-deploy-656c589d54-fvnf5 1/1 Running 0 22h
pod/search-deploy-656c589d54-t28m2 1/1 Running 0 22h
pod/search-function-deploy-85497fb7bc-6mph7 1/1 Running 0 22h
pod/search-function-deploy-85497fb7bc-wzrhx 1/1 Running 0 22h
pod/textanalytics-function-deploy-6884ccdb5b-2fch5 1/1 Running 0 22h
pod/textanalytics-function-deploy-6884ccdb5b-ccnzm 1/1 Running 0 22h
pod/visitreports-deploy-7d774598b6-dk6zs 1/1 Running 0 22h
pod/visitreports-deploy-7d774598b6-zx5ds 1/1 Running 0 22h
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/contactsapi ClusterIP 10.0.233.94 <none> 8080/TCP 23h
service/frontend ClusterIP 10.0.183.66 <none> 8080/TCP 22h
service/resourcesapi ClusterIP 10.0.64.143 <none> 8080/TCP 23h
service/searchapi ClusterIP 10.0.145.162 <none> 8080/TCP 22h
service/visitreportapi ClusterIP 10.0.148.56 <none> 8080/TCP 22h
NAME ENDPOINTS AGE
endpoints/contactsapi 10.244.0.40:5000,10.244.2.25:5000 23h
endpoints/frontend 10.244.1.19:80,10.244.2.32:80 22h
endpoints/resourcesapi 10.244.0.41:5000,10.244.2.26:5000 23h
endpoints/searchapi 10.244.0.42:5000,10.244.2.27:5000 22h
endpoints/visitreportapi 10.244.1.17:3000,10.244.2.28:3000 22h
NAME HOSTS ADDRESS PORTS AGE
ingress.extensions/ing-contacts 20-67-122-249.nip.io 20.67.122.249 80 23h
ingress.extensions/ing-frontend 20-67-122-249.nip.io 20.67.122.249 80 22h
ingress.extensions/ing-resources 20-67-122-249.nip.io 20.67.122.249 80 23h
ingress.extensions/ing-search 20-67-122-249.nip.io 20.67.122.249 80 22h
ingress.extensions/ing-visitreports 20-67-122-249.nip.io 20.67.122.249 80 22h
Some links given by the tutors for further reading
https://blog.crisp.se/wp-content/uploads/2012/11/SpotifyScaling.pdf





Thanks for reading, thanks Microsoft for this opportunity, thanks netzkern for letting me attend. Stay healthy friends.


